[SC-100] Azure Monitor Agent vs Log Analytics Agent
I came across a nifty article explaining the difference between the legacy Log Analytics Agent and Azure Monitor Agent.
There's some feature improvements in terms of what logs can be retrieved with AMA but I think the biggest notable difference is performance-related. As per Microsoft: "The Azure Monitor agent provides a . . .
[SC-100] Microsoft architectures - the bigger picture
There's a lot of Microsoft diagrams and workflows but this is by far my favorite:
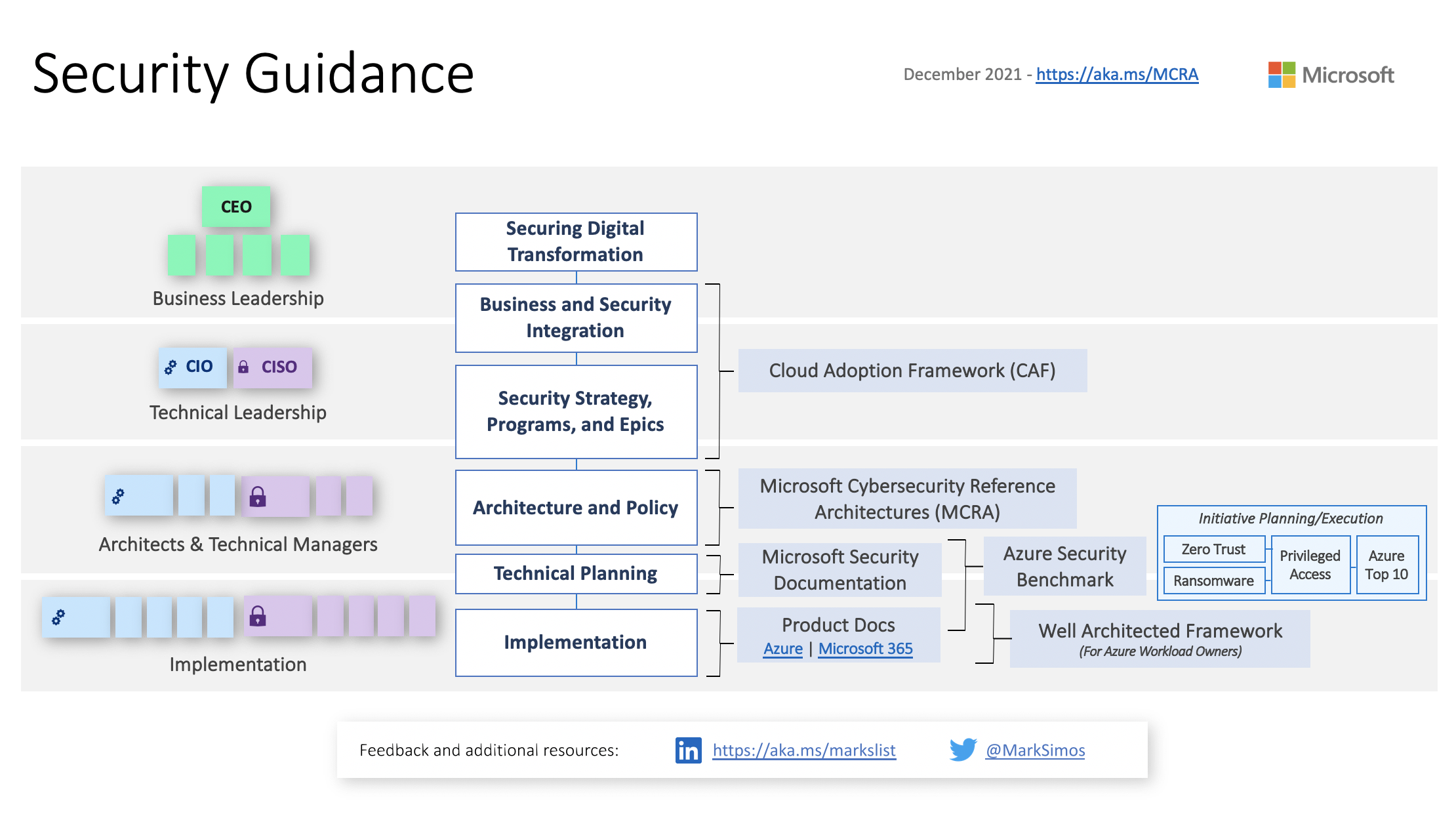
It's a bit dated (2021 feels like a lifetime ago) but the information is still absolutely relevant. This diagram illustrates how different Microsoft reference architectures, models, and resources apply to the various levels of . . .
[Sc-100] Technical Video Overview of MCRA
Because sometimes a video is worth a thousand slides.
In preparing for the SC-100 Microsoft exam, one frequently referenced resource I've come across is the Microsoft Cybersecurity Reference Architecture (MCRA). It's an absolutely brilliant set of concepts, architectures, diagrams, and workflows but there's just one issue: It's a bit of information overload.
I recently . . .
IoT Architecture Zones
I'm digging this illustration of IoT security architecture zones, courtesy of Microsoft docs.

The beauty of it all is the simple (but effective) principles:
- Segment the solution
- Minimize the impact of lower-trust zones against higher-trust zones
- Assume that as data traverses zones, it could be . . .
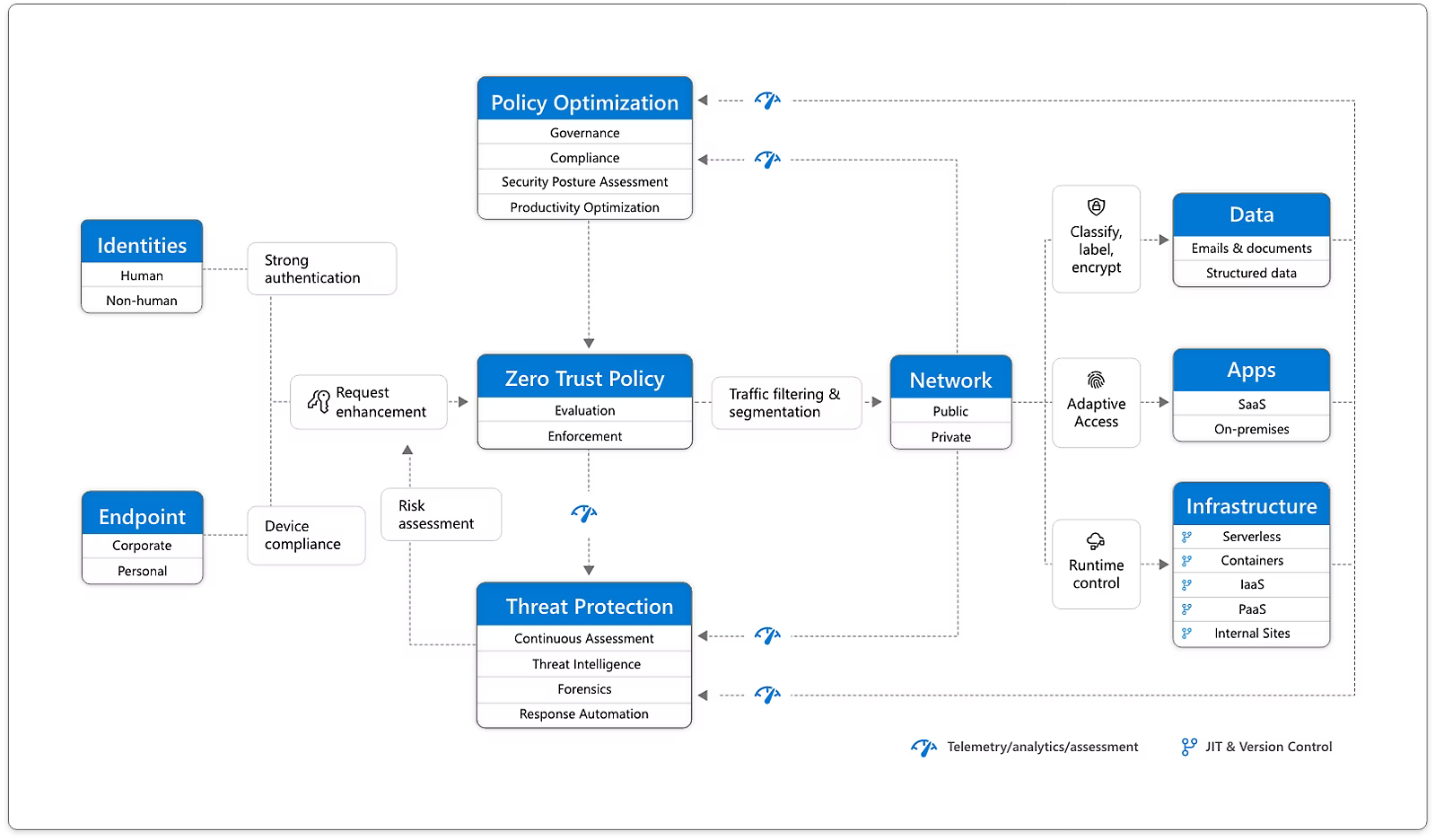
[SC-100 Exam Prep] Zero trust example workflow topology
A (zero trust) picture is worth a thousand words :-)
In preparing for the Microsoft SC-100 exam, I came across a nifty article from Microsoft regarding their position on Zero Trust.
Among other things, it includes a high-level example diagram of a topology combining a number of concepts.
Check it out: